The OPM breach has been deservedly in the news for over a month now. Much has been written and said about it across the mainstream media and the internet1.
I want to focus here on a topic that hasn’t necessarily been discussed in public, perhaps not at all – Could the OIG (and their audit reports) have done more or different than what they did, year after year of issuing the reports? Specifically, how could these audit reports have driven some urgently needed attention to the higher risks and perhaps helped prevent the breach?
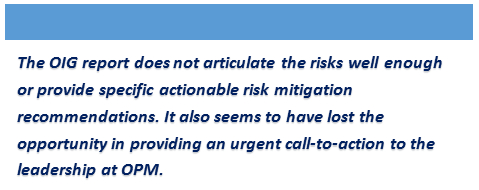
Let us look at the latest OIG’s Federal Information Security Management Act (FISMA) audit report issued in November 2014 (pdf) as a case in point. The report runs over 60 pages and looks to have been a reasonably good effort in meeting its objective of covering the general state of compliance with FISMA. However, I am not sure the report is any useful for “real world” risk management purposes at an agency that had known organizational constraints in availability of appropriate security people or resources; an agency that should have had some urgency in implementing certain safeguards on at least the one or two critical system(s) for the nature and quantity of sensitive information they had.
We have talked about this problem before, advising caution against “fixation” with compliance or controls frameworks and not focusing on priority risk management needs. In the case of this particular report, the OIG should have discussed the risks as well (and not just the findings or gaps) and provided some actionable prioritization for accomplishing quick-wins in risk mitigation. For example, recommendation #21 on page 25 could have called out the need for urgency in implementing multi-factor authentication (or appropriate compensating controls) for the one or two “high risk” system(s) that had upwards of 20 million sensitive records that we now know were breached.
I also believe providing a list of findings in the Executive Summary (on page 2) was a wasted opportunity. Instead of providing a list of compliance or controls gaps, the summary should have included specific call-to-action statements by articulating the higher risks and providing actionable recommendations for what the OPM could have done over the following months in a prioritized fashion.
Here then are my recommended takeaways:
- If you are an auditor performing an audit or a consultant performing a security assessment, you might want to emphasize “real” risks, as opposed to compliance or controls gaps that may be merely academic in many cases. Recognize that evaluation and articulation of risks require a more complete understanding of the business, technology and regulatory circumstances as compared to what you might need to know if you were merely writing gaps against certain controls or compliance requirements.
- Consider the organizational realities or constraints and think about creative options for risk management. Always recommend feasible quick-wins in risk mitigation and actionable prioritization of longer term tasks.
- Do not hesitate to bring in or engage with specialists if you aren’t sure you can evaluate or articulate risks and recommend mitigation tasks well enough. Engage with relevant stakeholders that would be responsible for risk mitigation to make sure they are realistically able to implement your recommendations, at least the ones that you recommend for implementation before your next audit or assessment.
In closing, I would strongly emphasize a focus on meaningful risk management outcomes, not just producing reports or deliverables. A great looking deliverable that doesn’t convey the relative levels of real risks and the urgency of mitigating certain higher risks is not going to serve any meaningful purpose.
References for additional reading
At the time of this writing, I found these two links to be useful reading for substantive information on the OPM breach.
Information about OPM Cybersecurity Incidents
“EPIC” fail—how OPM hackers tapped the mother lode of espionage data
You may also be interested in a quick read of our recommendations for agile approaches to security/privacy/compliance risk assessments or management. A pdf of our slide deck will be emailed to you after a quick registration here.
0 Comments