The California Consumer Privacy Act of 2018 (CCPA) is shaping up to be the most significant consumer privacy law passed in the United States in recent memory. The Act, which becomes operative on January 1, 2020, is modeled to a degree on certain provisions of the European Union’s General Data Protection Regulation (GDPR). The law requires the California Attorney General’s (AG) office to issue final regulations within six months from the law’s operative date. The law itself becomes enforceable by the AG starting six months from the date the final regulation is issued or by July 1, 2020, whichever is sooner.
One should watch out for further amendments to the law this year. It’ll also be interesting to see what’s in the final regulation to be issued by the AG. It appears that the proposed rule could be expected in Fall 2019 and the final rule (regulation) in due course of time thereafter.
As one would expect from a consumer privacy law, much of the content is focused on mandating privacy requirements based largely on the Fair Information Practices Principles.
While there has been considerable coverage and discussion around the law in general, a quick search on the Internet reveals that there isn’t nearly as much conversation around security safeguards that organizations must implement to meet CCPA requirements. Indeed, the law does not suggest use of any specific security controls or frameworks. On the other hand, it merely requires organizations to “implement and maintain reasonable security procedures and practices appropriate to the nature of the information to protect the personal information”.
The amendment to the law by Senate Bill 1121 also allows private right of action if an organization’s failure to implement and maintain “reasonable” safeguards results in a data breach. (CCPA § 1798.150(c))
The question that should arise then is what constitutes “reasonable” security safeguards. One hopes the AG will issue specific guidance as part of the rule making process underway, if they decide not to include specific details in the regulation itself. While I don’t recommend prescriptive security requirements to be included in any regulation (see the post in the context of HIPAA Security Rule), I do think that suitable guidance will be very helpful in the case of CCPA. I believe the guidance will be especially important, considering that the law allows for the private right of action.
As it turns out, the AG has somewhat of a precedent to draw upon from one of their own guidance from not so long ago. The California Data Breach Report 2012-2015 issued by the AG’s office in February 2016 has a very specific recommendation for what might be considered “reasonable” for security safeguards. It goes so far to recommend Center for Internet Security’s Critical Security Controls (CIS Controls) as the minimal and reasonable standard.
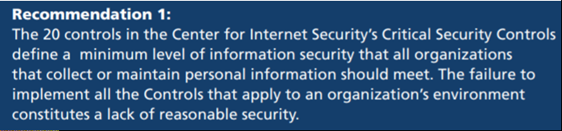
I believe the AG should issue guidance to highlight the same recommendation once again for what constitutes “reasonable” security safeguards in the context of CCPA.
I have discussed the use of CIS Controls in the past, here and here. As (still) perhaps the only set of controls that is “informed by current and evolving threats” and has a “bias for risk mitigation action”, I believe the CIS Controls would once again be a sound recommendation for what constitutes “reasonable” security safeguards.
Finally, this would be a good time for organizations and security/privacy professionals to engage with the AG and provide input in their rule making process. I’ll be looking to do so myself.
0 Comments